SANS FOR608 Enterprise-Class Incident Response & Threat Hunting
I recently took the SANS FOR 608 Enterprise-Class Incident Response & Threat Hunting course. Going into the course, I wasn’t super thrilled with my choice. This is the last class for me in the Incident Response program. At this point I’ve taken a lot of the other electives through other means. I also felt, by looking at what this course covered, I had already taken a good chunk of what would be covered in those other courses. However, I think if you are someone leading IR investigations or threat hunts in your org, this is a really solid course for you.
Day 1 focuses primarily on running these larger-scale investigations and engagements. Various tools you can use for data collection and collaboration. It really spends more focus time on what you should be doing as a leader of the investigation, not the actual analyst. I don’t think there is anything earth-shattering in here, and if you’ve been leading a lot of these engagements, you might pick up a few things or a slightly different way to think about what you are already doing.
Day 2 mostly focuses on how you do things at scale. This includes how you can leverage your existing EDR tools, Velociraptor and Elastic Stack. There is also a section around AI tools thrown in at the end. It’s quite good actually but feels a little out of place with the rest of the course. I don’t think I have any better ideas on where this section should live either.
Day 3 covers living off the land and some other additional advanced Windows techniques. The vast majority of this day is focused on Linux. This was one of the things I struggled with taking this course. If I really wanted to learn Linux DFIR, why don’t I just take FOR 577 Linux Incident Response & Threat Hunting? FOR 608 is about the altitude of where you are at. This is more for someone who needs to know the core things to think about and make sure the analysts are looking for when it comes to Linux. NOT to be the analyst yourself. That’s where I’m guessing FOR 577 will come in; that’s for the actual hands-on analyst.
Day 4 is split between macOS and containers. Very similar to the Linux section. It’s enough to know what to look for and give you an idea. If you want to get into the depth as an analyst, take the deeper courses. I had previously taken FOR 518 macOS and iOS Forensic Analysis and Incident Response, and as well as doing the whole cloud program, I touched containers a few times, so this was mostly review.
Day 5 focuses again on what you need to know for a cloud investigation in Microsoft 365 and AWS. This was mostly a review for me again.
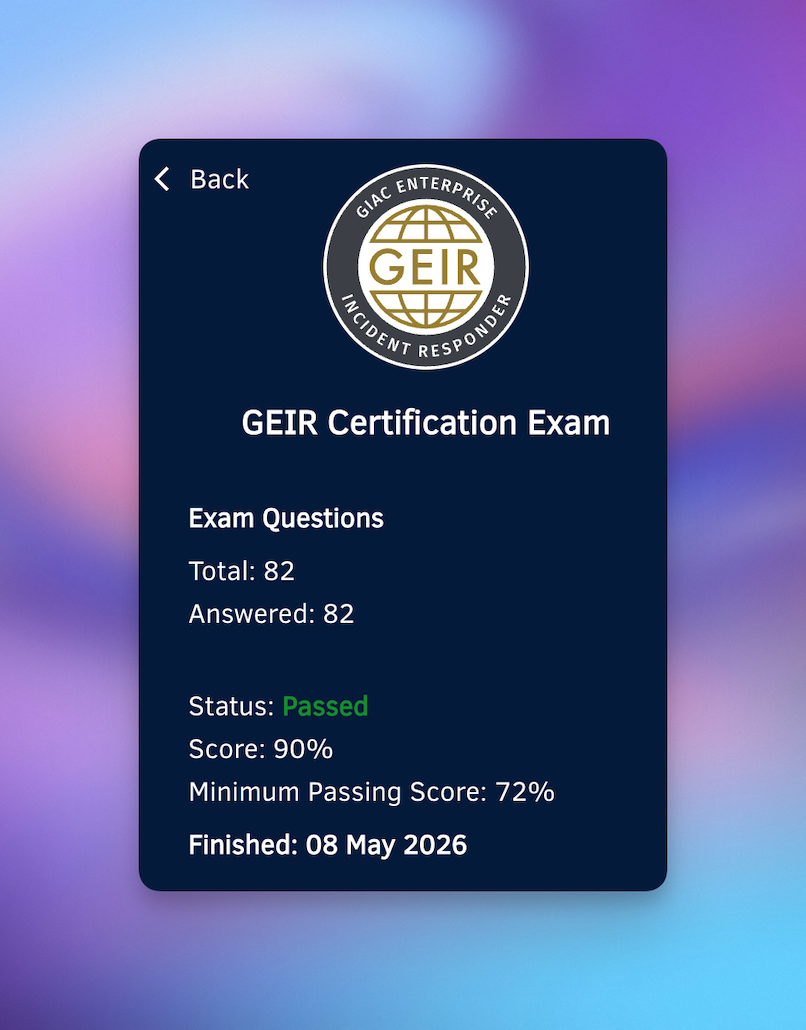
The practice tests were slightly easier than the exam. I scored a 90% to finish up my time in this program and probably my last SANS course for quite a while. This ended up being a lot better course for me than I expected, and I would recommend it for the more senior IR and threat hunting members or those that want to get some experience with the day 3, 4, and 5 material before taking the deep dive analyst-level course. I find, though, in my day-to-day, this course is more aligned with what I’m doing. This was probably the right course for me to take over my other choices I was thinking about (FOR 585, FOR 577, and FOR 509).
In summary, if you are leading IR investigations or threat hunts or you want to just cover a few other areas as an analyst in one course, this is a good choice. If you want to go deeply at the analyst level in macOS, Linux, and cloud, you should take those specific courses.
If you are interested in applying to the SANS EDU program, feel free to reach out with any questions, and I also have a referral code that removes the entrance fees. Happy to chat!